The rise of remote work has led many individuals to seek out budget-friendly coworking spaces that foster a sense of community. While you may find comfort working from home, consider exploring a coworking environment to enhance productivity and professionalism. However, it’s important to acknowledge the potential risks associated with coworking spaces, such as increased susceptibility to cyber theft, malware, and other malicious activities. Take proactive measures to safeguard your data against cybercrime and maintain coworking privacy.

Why Coworking May Not Be Secure?
Public WiFi networks that are password-protected may create a false sense of security, but they are not entirely safe. Even if each user has a unique login, it is unwise to assume that your privacy is guaranteed. Let’s explore the basics of WiFi in coworking spaces to better understand cybersecurity risks.
Firstly, most coworking spaces use the WPA2-PSK security protocol for their WiFi. WPA2 is a security standard that protects devices connected to wireless networks. It was designed to address vulnerabilities found in the previous standard, WEP. In theory, WPA2 provides more robust security with strong encryption and authentication certification. However, it is not foolproof.
Hackers can use network sniffing programs like WireShark to intercept and decode information transmitted within the coworking space. All they need to do is sign up as a user, connect to the network, and run the sniffing application. Moreover, tutorials on intercepting WPA2-PSK data packets are readily available online.
Some coworking spaces may have upgraded to the newer WPA3 password security protocol. Despite its security enhancements, WPA3 still has vulnerabilities that expose users to man-in-the-middle attacks. In these attacks, hackers redirect users to fraudulent websites that steal their data.
Main vulnerabilities
Connecting to WiFi at your coworking space without additional protection exposes you to cyberattacks. These include:
- Competitors intercepting sensitive files shared across the network or retrieving them from unsecured folders.
- Hackers redirect you to fake websites that mimic legitimate ones, where you unknowingly enter sensitive information like banking credentials.
- Easier infection of computers with malicious programs such as ransomware and malware, disrupting by threatening to delete files unless a ransom is paid.
- Perpetrators launch targeted attacks that exploit software vulnerabilities on specific computers by accessing your exposed private and public IP addresses.
What is the role of a VPN?
To improve the security of your workplace, you need a VPN. While traditional encryption protects data while it is stored on a server or in device memory, a VPN provides encryption while it is in transit. These are not monofunctional utilities; they are useful for other purposes.
For example, you can use a VPN for Netflix to unblock available content. You will also have to figure out a little how to change the Netflix region. All you need is VeePN for Netflix and a few minutes. VeePN will help you change your IP address, and this is the main component of the success of the planned procedure.
Using a VPN in a coworking space is a smart move to safeguard your devices and data, preventing potential cyber fallout. A VPN offers robust security by hiding your device’s IP address and encrypting all data transmissions. By accessing coworking WiFi via a VPN, you significantly reduce the risk of cyberattacks. Hackers struggle to target your computer without your IP address, and even if they manage to do so, the encrypted data remains unreadable. This effectively blocks targeted attacks, industrial spying, and other snooping attempts.
Additional Protection Methods
#1 Use Encryption
Passwords act as gate passes to enter the vast realm of cyberspace—both for regular users and for cyber bullies and criminals. Sadly, recent advancements in hacking technology have rendered traditional passwords ineffective.
To safeguard your data effectively, particularly in shared coworking environments with shared internet access, you need to take an extra step with data encryption.
Creating an active firewall and engaging in end-to-end data encryption may seem like advanced cybersecurity measures, but they guarantee restricted access to your data. Only authorized individuals can view or modify it.
#2 Keep Software Up to Date
Tech manufacturers often prioritize new software updates for their devices, neglecting older versions and leaving potential vulnerabilities for malware. This issue is especially prevalent among major tech companies that have numerous devices to support.
At times, users are alerted and urged to download updates, but occasionally, they are left unaware, putting their data at risk. Failing to update your devices and apps to the latest versions can leave them susceptible to malware and hackers.
#3 Use Two-Factor Authentication
Working from a shared office to boost productivity can significantly increase the likelihood of a data breach due to compromised passwords. It is strongly recommended to avoid passcodes that can be easily deduced, such as those based on birthdays or anniversaries. Instead, opt for a combination of uppercase and lowercase letters, numbers, and symbols generated by reputable password tools. However, it’s important to note that even a strong password might not always deter skilled hackers. For this reason, two-factor authentication, also known as two-step verification, has been introduced. This process requires users to verify their login attempts by entering a code sent to their phone number or email, even after submitting their passwords.
Conclusion
When working in a coworking space, you are solely responsible for safeguarding your data, unlike in a traditional office where a cybersecurity team handles office security. Coworking spaces offer enticing benefits like a sense of community, shared networks, and a unique “in-the-office-though-out-of-the-office” feel. However, these perks also present opportunities for unintentionally compromising sensitive data. In such conditions, a VPN is simply necessary so that no one can intercept your data or attack your device.


 How to Choose the Right AI Video Generator: Model and Use Case Analysis
How to Choose the Right AI Video Generator: Model and Use Case Analysis  How to Choose the Right GenAI Partner for Your Business in 2026
How to Choose the Right GenAI Partner for Your Business in 2026 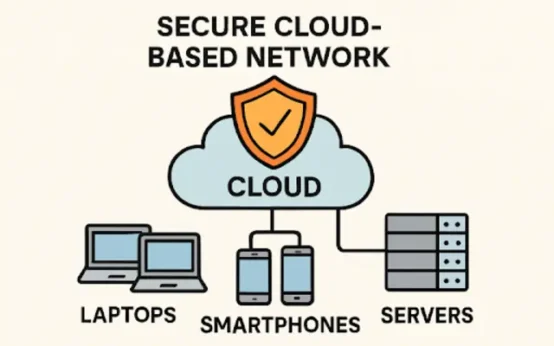 Practical Strategies for Building Reliable Network Security in a Cloud-First World
Practical Strategies for Building Reliable Network Security in a Cloud-First World  DeepSeek R1: The AI Revolution That Defied U.S. Trade Barriers and Stunned the World
DeepSeek R1: The AI Revolution That Defied U.S. Trade Barriers and Stunned the World  Why Some AI Models Fail Under Pressure – A DeepSeek AI Case Study
Why Some AI Models Fail Under Pressure – A DeepSeek AI Case Study  Various Ways to Sell Bitcoin for Cash Instantly
Various Ways to Sell Bitcoin for Cash Instantly